Dataset Source - Microsoft Azure Blob Storage
Attach Blob Storage Container
You can easily attach a Microsoft Azure Blob Storage container to your project -
- Add the Azure Tenant ID.
- Add the Azure Storage Account Name.
- Add the Azure Blob Storage container name.
- Add a folder prefix (optional).
- Add permissions in your Azure Container Bucket as outlined, Add Permission for Azure MD.ai Application section introduces how to add permission in detail.
- Confirm Container permissions once added.
- Press
Connect.
Add Permission for Azure MD.ai Application
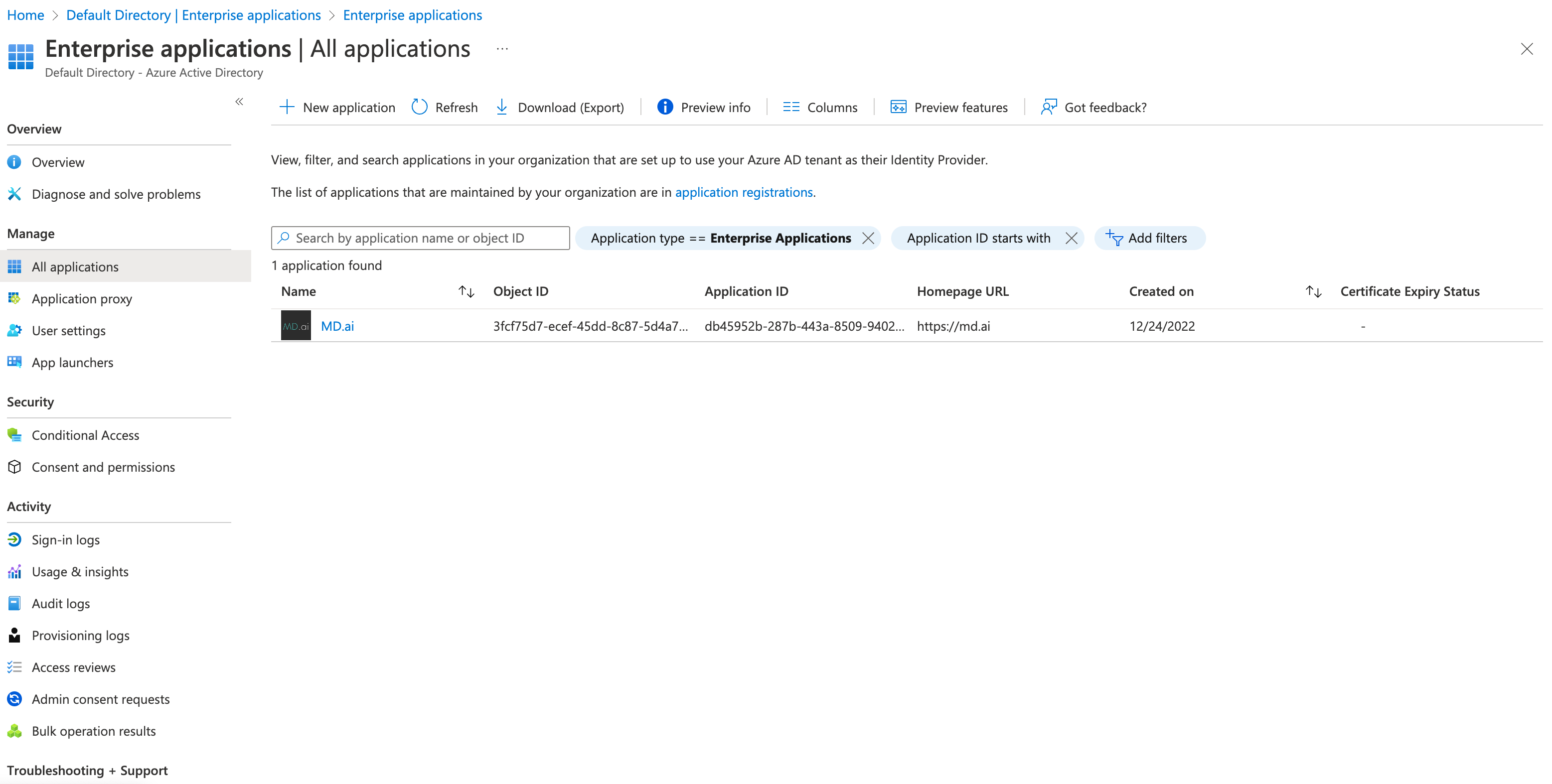
MD.ai service uses Azure MD.ai application [Application ID: db45952b-287b-443a-8509-9402266814db] to load data from Azure Blob Storage container, it is required to add proper role assignment for it. You can also click Role Assignment Update Guide button to check how to add permission when edit dataset.
There are two steps to add permission:
Step 1: Consent Application
Click link in Role Assignment Update Guide panel and consent Azure MD.ai application to the tenant.
Note
You need proper Tenant role to consent application.
After consent, Azure MD.ai Application would in the tenant's Enterprise Applications list.
Step 2: Add Role for Application
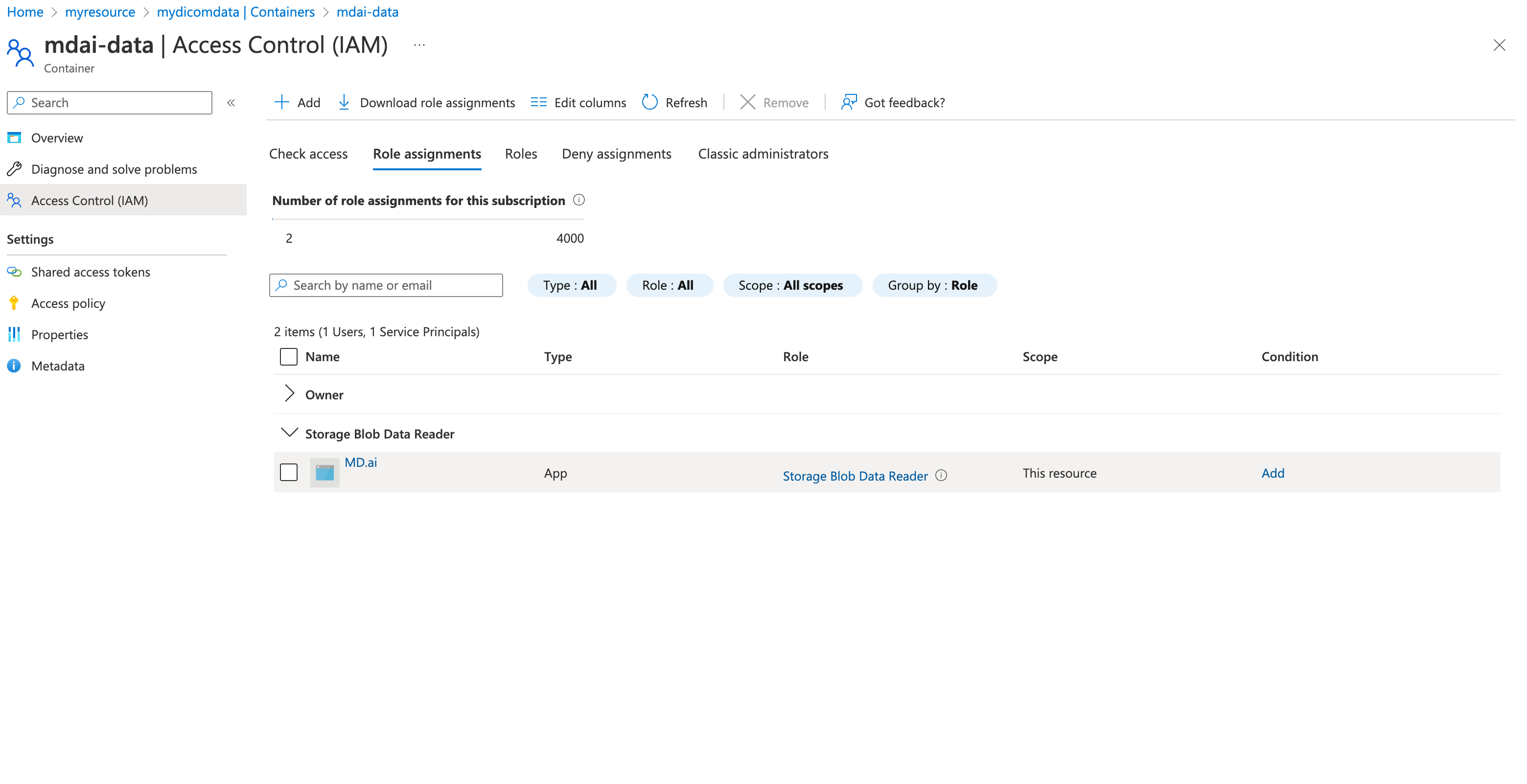
Add Storage Blob Data Reader role for Azure MD.ai application for which consent was added in Step 1. The Role Assignment Update Guide panel provides an Azure CLI template, replace some mock IDs (MDAI_APPLICATION_OBJECT_ID_IN_YOUR_TENANT, YOUR_SUBSCRIPTION_ID, YOUR_RESOURCE_GROUP_NAME) with your own ones, and execute the command to add required role assignment.
For required MD.ai application Object ID (MDAI_APPLICATION_OBJECT_ID_IN_YOUR_TENANT), you can find it in the tenant's Enterprise Applications list.
Once role assignment is added, Azure MD.ai application would show up in associated Blob Storage container's Access Control (IAM) role assignments list.